Bridging Security Gaps: A Practical Comparison of Leading Vulnerability Scanners
A deep dive into authenticated vs. non-authenticated scans with Nessus and OpenVAS against intentionally vulnerable systems — key findings and practical takeaways for security professionals.
Bridging Security Gaps: A Practical Comparison of Leading Vulnerability Scanners
A Deep Dive into Authenticated vs. Non-Authenticated Scans with Nessus and OpenVAS
I'm thrilled to share a personal cybersecurity project that stemmed from one of the final exercises in the "Cibersegurança — Vetores Ataque e Métodos Proteção" course at Cesae Digital — Centro para o Desenvolvimento de Competências Digitais. This hands-on experience was incredibly insightful. I extend a massive thank you to Professor Daniel A. Melo and my fellow classmates; their invaluable insights and shared learning experiences truly enriched this journey.
Project Objective
The primary goal of this exercise was twofold:
- Compare Scan Methodologies: Evaluate the effectiveness of authenticated versus non-authenticated vulnerability scans, explicitly highlighting the critical importance of robust credential management policies in cybersecurity.
- Benchmark Scanning Tools: Benchmark a leading commercial solution, Tenable's Nessus, against its powerful open-source counterpart, Greenbone's OpenVAS, assessing their detection capabilities in a controlled environment.
The Test Environment
For this analysis, I utilized two virtual machines pre-configured with specific vulnerabilities and generously provided by Professor Daniel Melo:
| Host | Operating System | IP Address |
|---|---|---|
| Host 1 | Windows Server 2008 R2 | 192.168.56.16 |
| Host 2 | Ubuntu 14.04 LTS | 192.168.56.6 |
+--------------------------+ +-----------------------------+
| Virtualized Environment | | |
| | | |
| +--------------------+ | | +--------------------+ |
| | Windows 2008 R2 | | | | Ubuntu 14.04 LTS | |
| | VM | | | | VM | |
| | IP: 192.168.56.16 | | | | IP: 192.168.56.6 | |
| +--------+-----------+ | | +------------+-------+ |
| | | | | |
| +--------------+--------+---------------+ |
| Virtual Switch/Router |
| | |
| +-----------+-------------+ |
| | Scanning Machine | |
| | (Nessus / OpenVAS) | |
| +-------------------------+ |
+-----------------------------------------------------------------+
Vulnerability Scanning Tools Used
The project leveraged both industry-leading commercial software and a robust open-source alternative:
- Nessus Trial (Tenable): Version 10.9.0 (#144). The trial version, while limited in IP scanning, provided a powerful glimpse into its capabilities.
- OpenVAS (Greenbone Security Assistant — GSA): Version 25.0.0 with updated feeds:
- NVT: 20250703T0642
- SCAP: 20250702T0508
- CERT: 20250703T0417
- GVMD_DATA: 20250703T0508
Scan Results
Nessus — Authenticated Scan
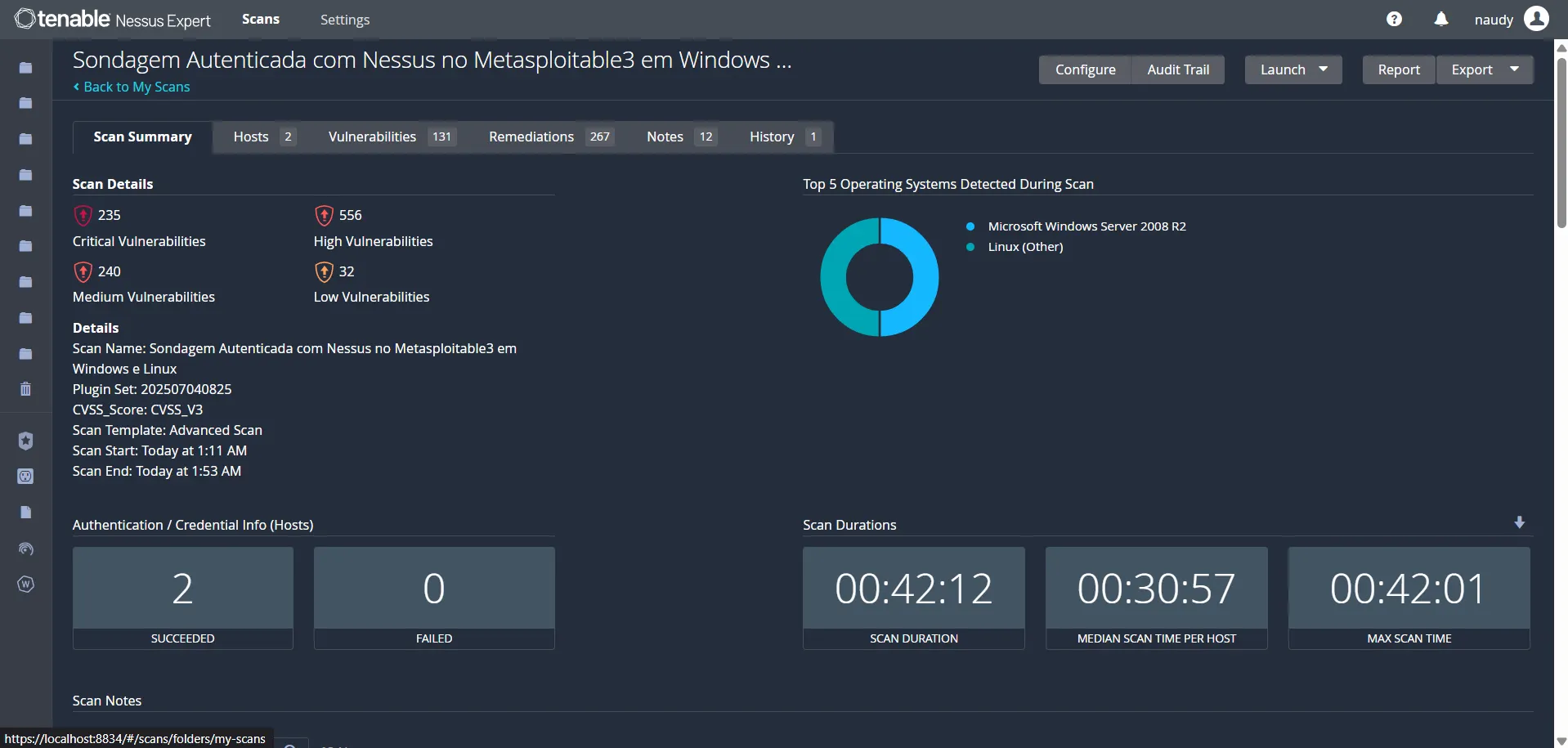 Nessus Scan Summary: 235 Critical, 556 High, 240 Medium, 32 Low — completed in 42 minutes with credentials
Nessus Scan Summary: 235 Critical, 556 High, 240 Medium, 32 Low — completed in 42 minutes with credentials
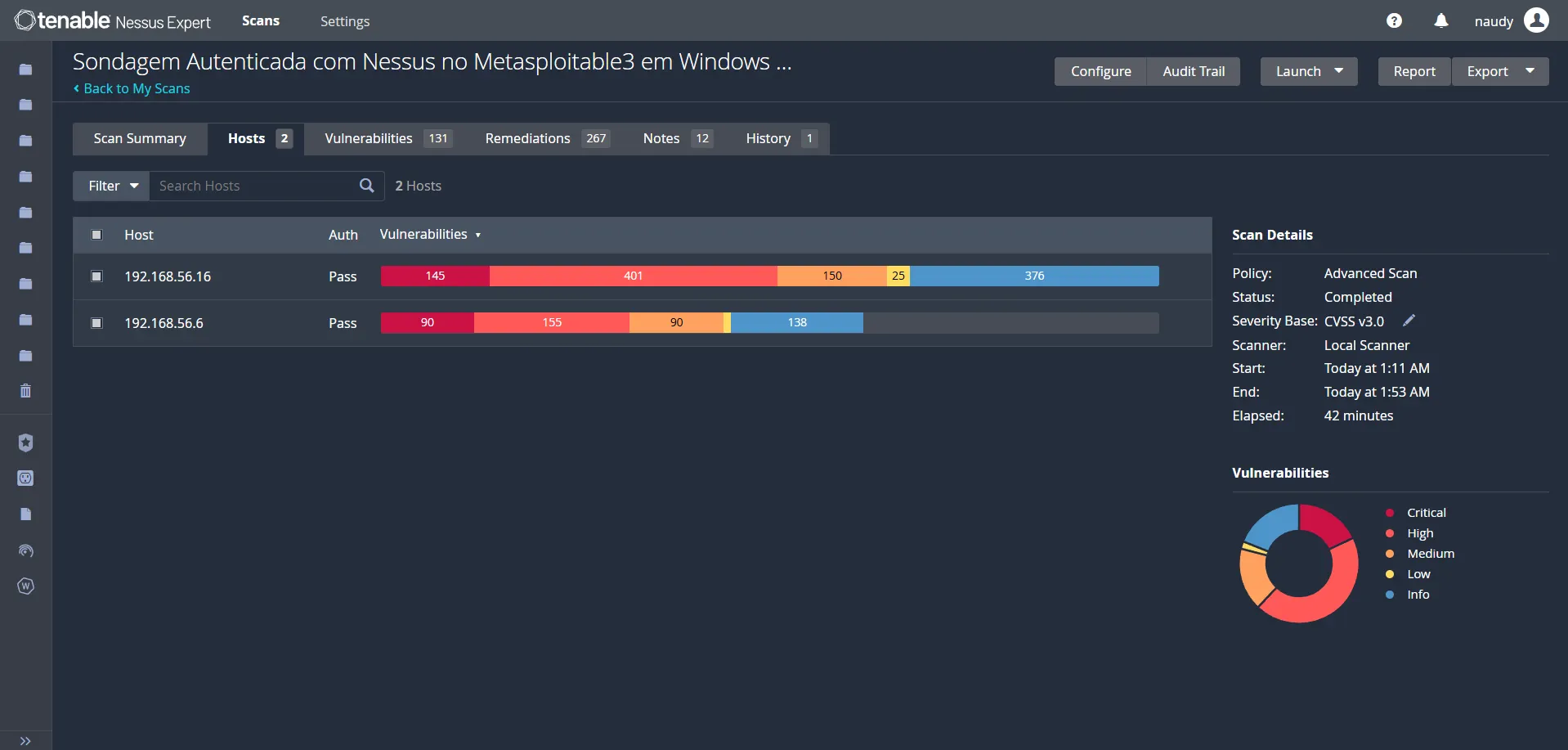 Nessus authenticated hosts: Auth=Pass on both — deep internal vulnerability exposure visible
Nessus authenticated hosts: Auth=Pass on both — deep internal vulnerability exposure visible
With credentials supplied, Nessus authenticated successfully to both hosts (Auth = Pass) and performed a deep internal scan. Plugin Set: 202507040825, CVSS v3, Advanced Scan template. Both hosts authenticated in 2/2 — 0 failures.
Results: 235 Critical · 556 High · 240 Medium · 32 Low Duration: 42 minutes (00:42:12)
Nessus — Non-Authenticated Scan
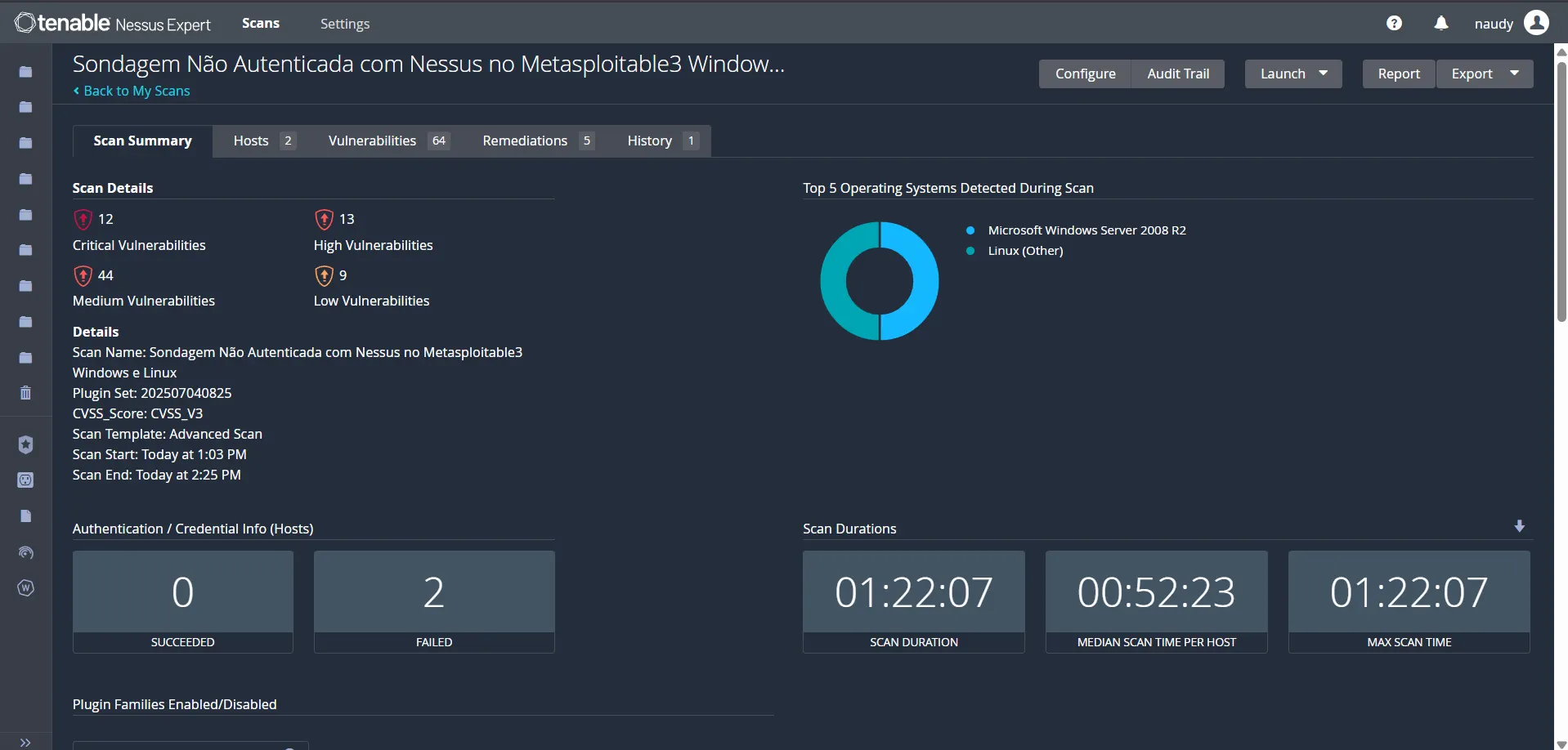 Nessus Scan Summary without credentials: only 12 Critical and 13 High — the external attacker view
Nessus Scan Summary without credentials: only 12 Critical and 13 High — the external attacker view
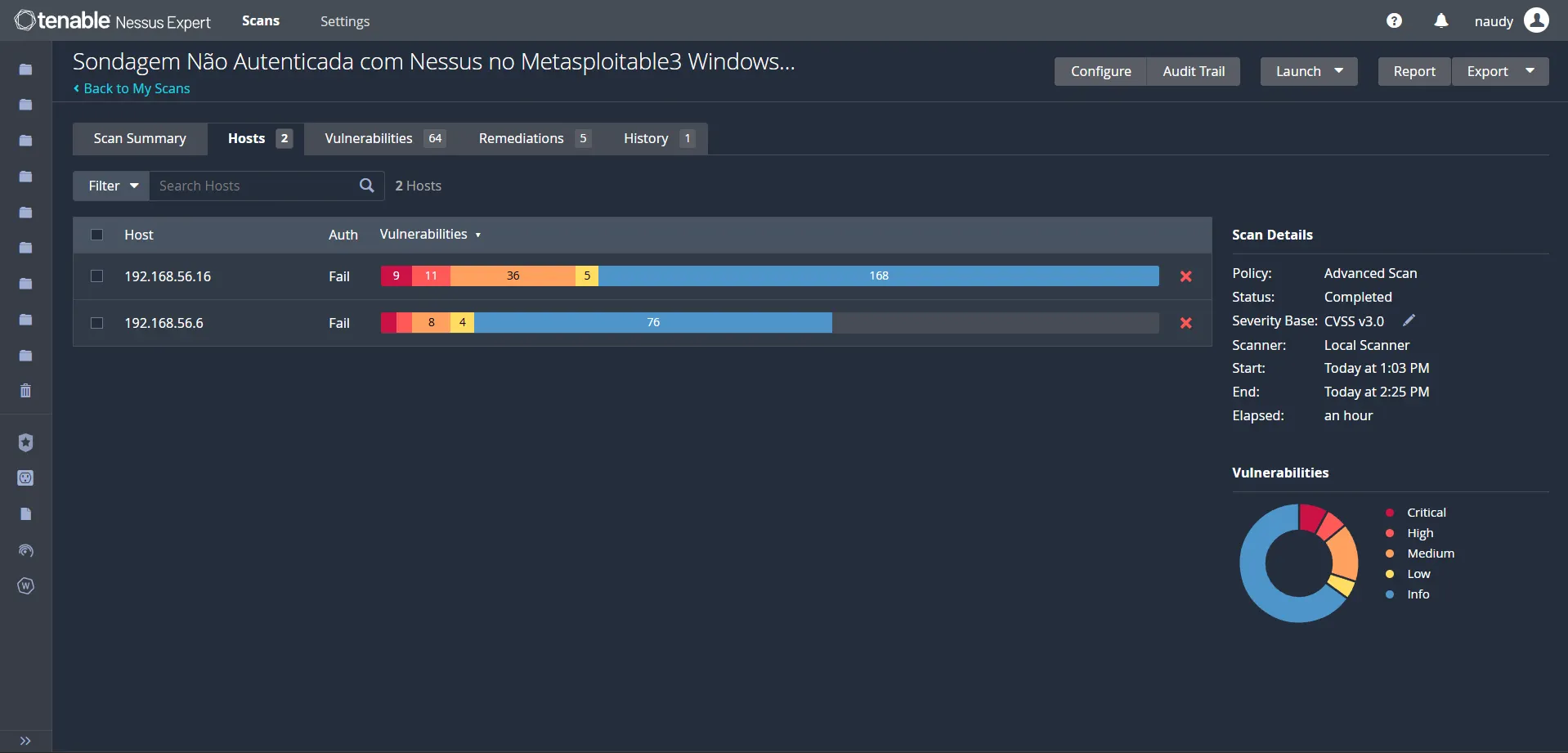 Nessus unauthenticated hosts: Auth=Fail on both — drastically reduced attack surface visibility
Nessus unauthenticated hosts: Auth=Fail on both — drastically reduced attack surface visibility
Without credentials, authentication failed on both hosts (Auth = Fail). The scan could only see what an external attacker without credentials sees — a fraction of the actual attack surface.
Results: 12 Critical · 13 High · 44 Medium · 9 Low = 78 total Duration: 1 hour 22 minutes (01:22:07)
OpenVAS — Authenticated Scan
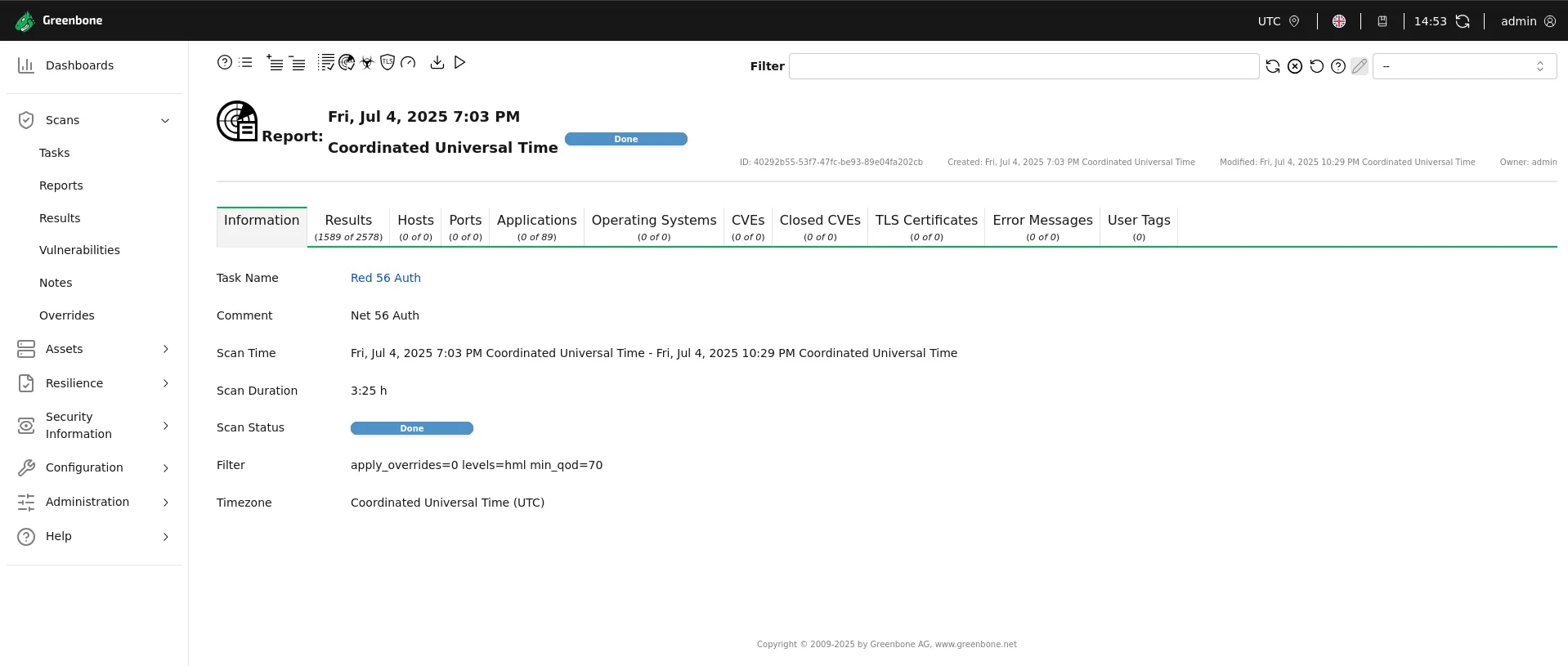 OpenVAS Report — Task "Red 56 Auth": 3h 25min scan duration, Done
OpenVAS Report — Task "Red 56 Auth": 3h 25min scan duration, Done
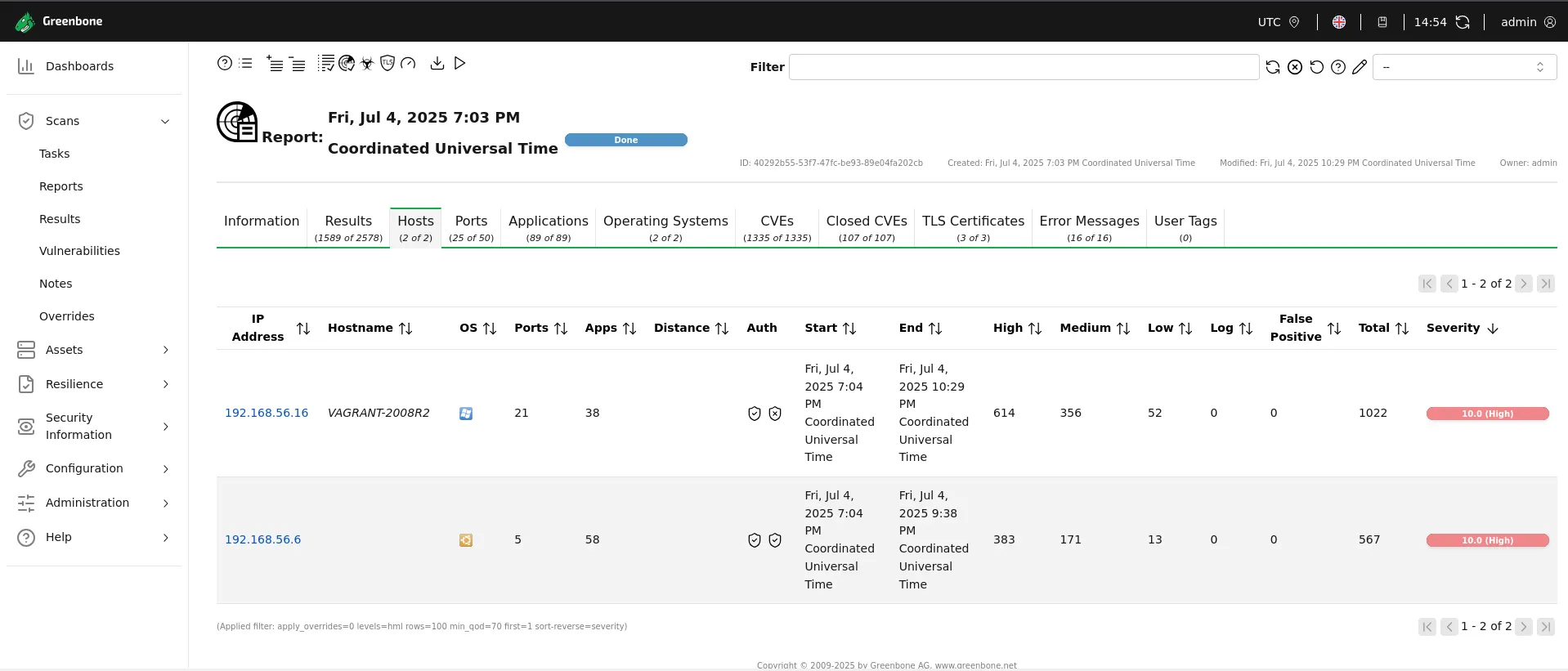 OpenVAS authenticated hosts: per-host breakdown showing 1,022 and 567 findings respectively
OpenVAS authenticated hosts: per-host breakdown showing 1,022 and 567 findings respectively
The OpenVAS authenticated scan ("Red 56 Auth") ran from 7:03 PM to 10:29 PM UTC (July 4, 2025). With credentials, it reached deep internal configurations on both hosts.
| Host | High | Medium | Low | Total |
|---|---|---|---|---|
| 192.168.56.16 (Windows) | 614 | 356 | 52 | 1,022 |
| 192.168.56.6 (Linux) | 383 | 171 | 13 | 567 |
| Total (min_qod ≥ 70) | 997 | 227 | 13 | ~1,237 |
Results filtered with min_qod=70 (Quality of Detection ≥ 70%), excluding low-confidence findings.
Duration: 3 hours 25 minutes
OpenVAS — Non-Authenticated Scan
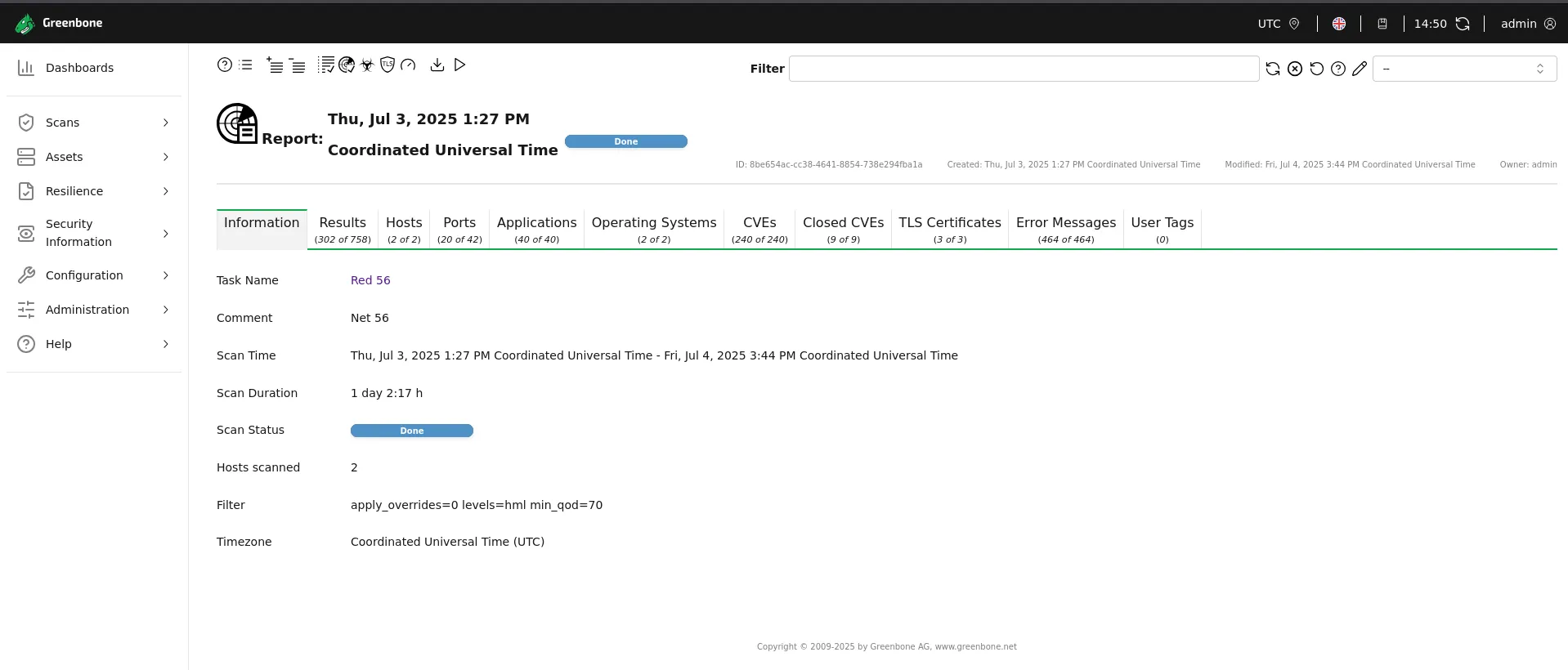 OpenVAS Report — Task "Red 56": 1 day 2:17h scan duration — a stark reminder of OpenVAS's external-scan cost
OpenVAS Report — Task "Red 56": 1 day 2:17h scan duration — a stark reminder of OpenVAS's external-scan cost
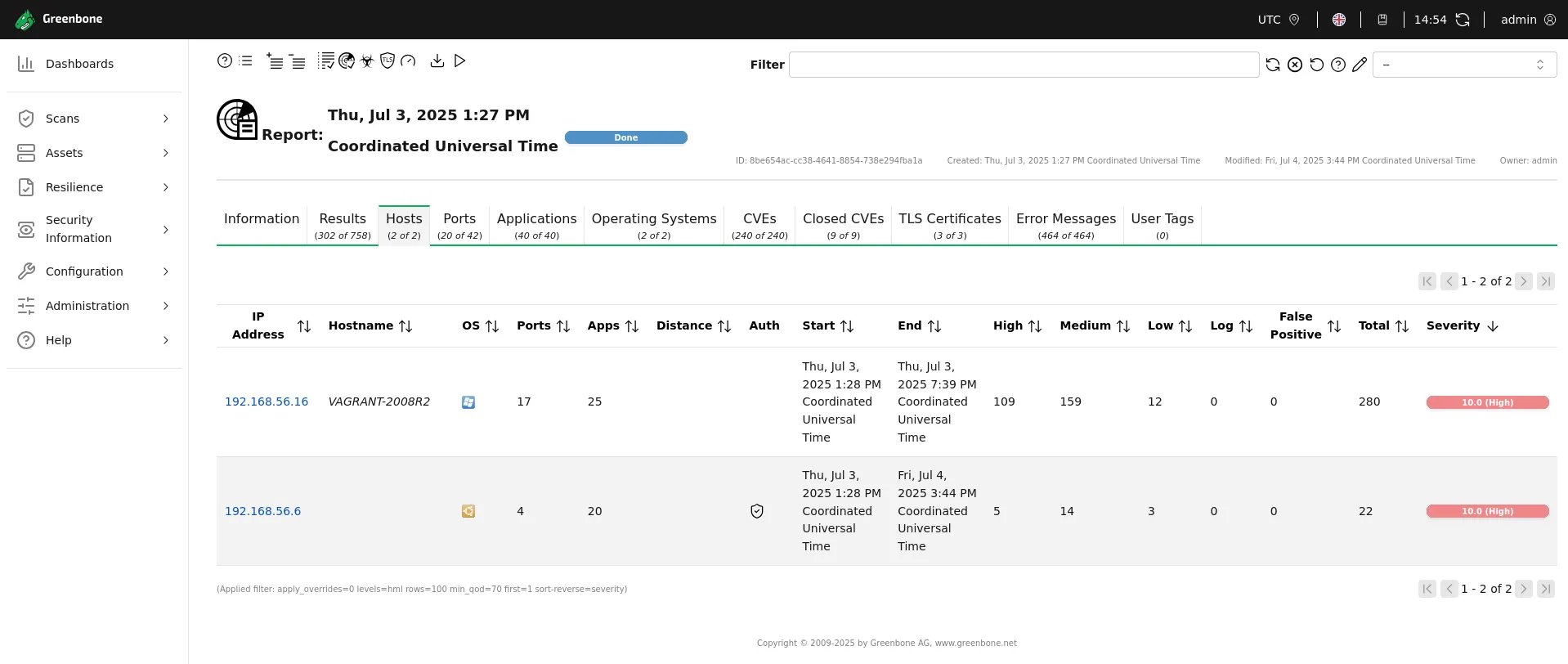 OpenVAS unauthenticated hosts: drastically fewer findings without credentials
OpenVAS unauthenticated hosts: drastically fewer findings without credentials
The unauthenticated OpenVAS scan ("Red 56") ran from July 3 to July 4, 2025 — an extraordinary duration that underlines OpenVAS's network-heavy external scanning approach.
| Host | High | Medium | Low | Total |
|---|---|---|---|---|
| 192.168.56.16 (Windows) | 109 | 159 | 12 | 280 |
| 192.168.56.6 (Linux) | 5 | 14 | 3 | 22 |
| Total (min_qod ≥ 70) | 114 | 26 | 3 | ~143 |
Duration: 1 day 2 hours 17 minutes
Key Findings & Significant Differences
The Power of Authentication
Both tools demonstrated vastly superior detection when provided with valid credentials. The numbers speak clearly:
- Nessus Authenticated: 1,063 vulnerabilities (235 critical, 556 high) in 42 minutes
- Nessus Non-Authenticated: Only 78 total (12 critical, 13 high) — 13× fewer
- OpenVAS Authenticated: ~1,237 combined (670 on Host 1, 567 on Host 2)
- OpenVAS Non-Authenticated: ~143 combined (121 on Host 1, 22 on Host 2) — 8× fewer
The internal, authenticated perspective provides a much deeper and more accurate assessment of a system's true security posture.
Full Comparison
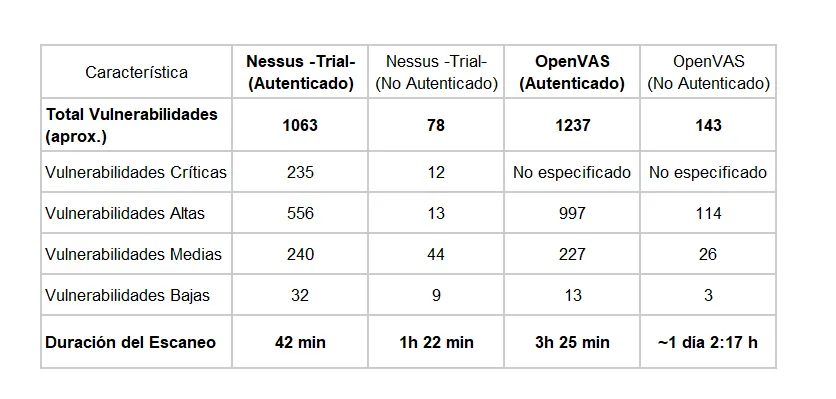 Complete comparison: authenticated vs. non-authenticated across both tools
Complete comparison: authenticated vs. non-authenticated across both tools
| Characteristic | Nessus (Auth) | Nessus (No-Auth) | OpenVAS (Auth) | OpenVAS (No-Auth) |
|---|---|---|---|---|
| Total Vulnerabilities | 1,063 | 78 | ~1,237 | ~143 |
| Critical | 235 | 12 | — | — |
| High | 556 | 13 | 997 | 114 |
| Medium | 240 | 44 | 227 | 26 |
| Low | 32 | 9 | 13 | 3 |
| Scan Duration | 42 min | 1h 22min | 3h 25min | ~1d 2:17h |
Nessus vs. OpenVAS Performance
Beyond detection numbers, performance metrics also varied significantly:
- Speed: Nessus was considerably faster in both modes — 42 min (auth) vs 3h 25min for OpenVAS; 1h 22min (no-auth) vs ~26 hours for OpenVAS.
- Detection Depth: Both tools found comparable totals with authentication (~1,000–1,237 vulnerabilities). Nessus reported more critical/high severity findings; OpenVAS delivered a substantial number of highs and mediums.
- OpenVAS External Cost: The non-authenticated OpenVAS scan taking over 26 hours is a practical consideration — resource planning is essential.
Insights & Recommendations
1. Authentication is Absolutely Crucial
For an accurate and comprehensive assessment, performing scans with authentication is indispensable. Authenticated tools access deeper system information — configurations, installed patches, running services — revealing the full internal attack surface. Unauthenticated scans show only the external view; authenticated scans show reality.
2. The Imperative of Strong Password Management
My findings reinforce that managing strong, unique, and uncompromised credentials is vital. Organizations must enforce policies for high-entropy passwords. Leveraging a robust password manager is essential for generating and storing unique credentials, monitoring for breaches, and enabling rapid rotation if a compromise is detected. This is often the fundamental first line of defense.
3. Open-Source as a Formidable Powerhouse
OpenVAS stands as a formidable open-source alternative. While it presents a steeper learning curve and generally requires longer scan times, its capability to detect a significant number of vulnerabilities (especially with authentication) makes it invaluable for organizations with budget constraints or a preference for open-source solutions.
4. Strategic Tool Selection is Key
The choice between commercial solutions like Nessus and open-source alternatives like OpenVAS should align with organizational factors: budget, need for professional support, interface familiarity, and existing infrastructure.
- Nessus: Greater speed and streamlined reporting — ideal for larger enterprises needing efficiency at scale.
- OpenVAS: Robust capabilities at zero license cost — ideal for organizations with technical staff and budget constraints.
5. Continuous Updates & Validation are Paramount
Regardless of the chosen tool, consistently keeping vulnerability databases (feeds/plugins) updated is crucial for detecting the latest threats. Always validate high-severity findings to confirm exploitability and avoid unnecessary actions based on potential false positives.
Conclusion
This hands-on project has further solidified my commitment to proactive vulnerability management. It vividly highlights the strategic role that both commercial and open-source tools play in securing digital assets — provided they are utilized with the correct methodologies and a deep understanding of their capabilities.
The single most impactful takeaway: the 13× difference between authenticated and non-authenticated Nessus scans. No scanner compensates for poor credential management. The tool is only as effective as the methodology behind it.
I'm always eager to discuss detailed technical reports or share more insights about this project. Feel free to connect!
Published as part of coursework at Cesae Digital — Centro para o Desenvolvimento de Competências Digitais. Special thanks to Professor Daniel A. Melo and fellow classmates for enriching this learning journey.
Originally published on Medium.